Sample of QR code for a mobile phone:

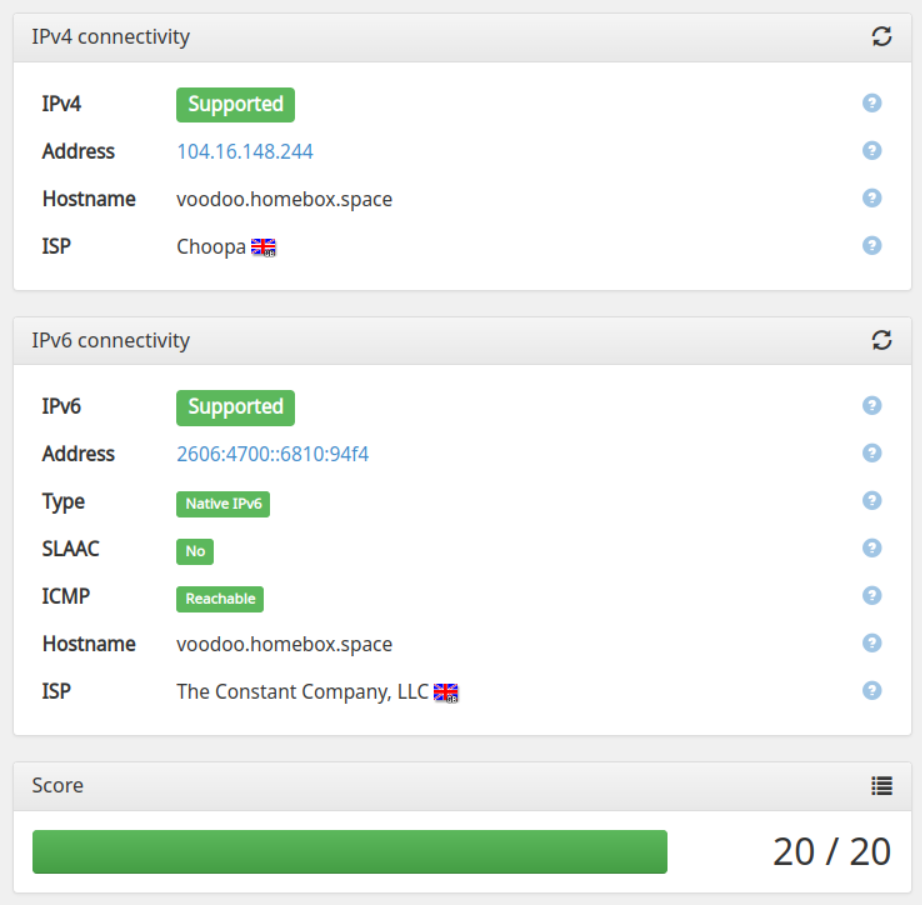
The VPN server can be configured to route all the traffic from the client, or to restrict the traffic to the server itself. In both case, both IPv4 and IPv6 addresses are fully supported.
Also known as split tunneling, this mode only enforce the VPN to access the server services, the other traffic goes through the client’s standard gateway.
In this mode, all the traffic is passing through the server, completely hiding the client IP address.
Once the VPN is installed, you can the configure some of the system services, like postfix submission, dovecot imap and pop3 access, jabber, grafana, webdav, etc... to be only accessible through the VPN. While these services are secure, exposing them on internet sometimes generate a lot of traffic from bots trying various password brute force attacks.
This is also protecting you if your server is targetted by more advanced attacks methods, like zero-day or unknown vulnerabilities.
Some internet service providers are a fittlering or even altering DNS answers, or sometimes enforcing their specific DNS servers, notoriously insecure. The DNS server used by the VPN validates DNSSEC records, does not alter the responses, and does not share access logs with any government organisation.
When running the playbook, the client configuration files are generated in the archives folder for each user, therefore, accessible through any WebDAV client.

The VPN also offers you static IP addresses, both in IPv4 and IPv6, which can be useful when you need
one. The support for IPv6 is complete and does not require any specific configuration, on desktop or on a
mobile phone.